Commodity Ransomware is Here. Brian Krebs recently posted a blog on a… | by Paul Kurtz | TruSTAR Blog | Medium

A Tale of Two Markets: Investigating the Ransomware Payments Economy | August 2023 | Communications of the ACM

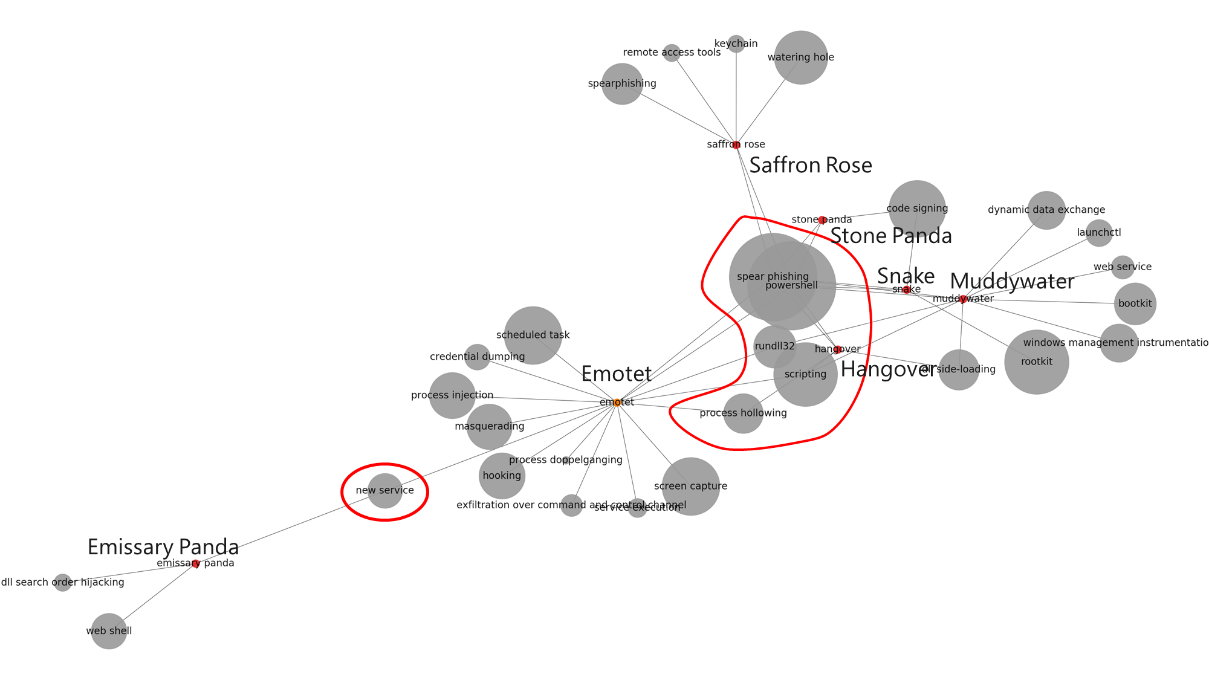
The distribution of targeted and commodity malware with respect to the... | Download Scientific Diagram

A Tale of Two Markets: Investigating the Ransomware Payments Economy | August 2023 | Communications of the ACM